Dragino -NB/-CB device connection to AWS platform instructions
Table of Contents:
- 1. Log in to the platform and find IoT core
- 2. Create your own test policy
- 3. Create a Things
- 4. Connect to AWS using Dragino-NB device
- 5. Configure draginoNB-device
- 6. View data on AWS
1. Log in to the platform and find IoT core
2. Create your own test policy
2.1 First click the policy on the left, enter the page and click Create policy

2.2 After filling in a policy name for testing, the policy will be displayed on the page
a. Fill in any name
b. Fill in * to Policy action and Policy resource (* stands for all)

c. After clicking to enter the policy configuration page, follow the clicking sequence below to go to the json configuration interface, and then fill in the following fields in the "statement" keyword:
{
"Version": "2012-10-17",
"Statement": [
{
"Effect": "Allow",
"Action": "iot:*",
"Resource": "*"
}
]
}

d. Create this policy
3. Create a Things
3.1 Create a single Things
1. Select Create Things


2. Fill in the name of the control item you want to create in the thing name column
Use the default for other parameters
Then click Next.

3. Choose to automatically generate a new certificate
Then click Next

4. The next step is to choose a strategy
Here you can choose a policy we created in the first step

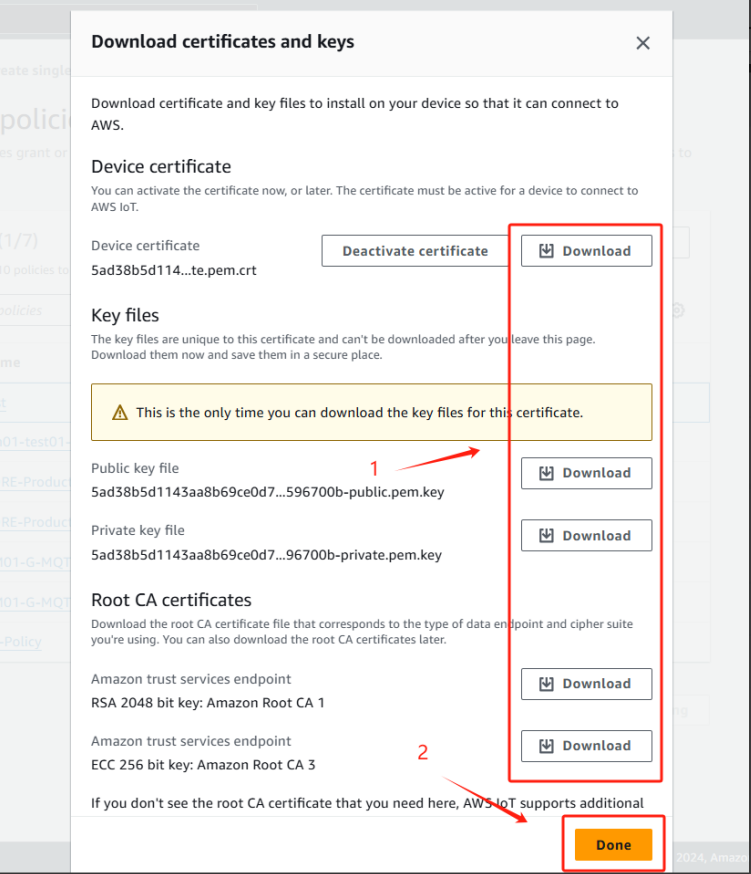
5. When you click to create things, the certificate download page will pop up
This certificate is very important. After creating the device, you must download the certificate of the device so that our NB device can connect normally.
Please download all the following certificates and put them in a folder.
6. You can see the things you just created in the things

4. Connect to AWS using Dragino-NB device
Note: In order to avoid problems with certificate writing, you need to set the serial port assistant to automatically add a newline character when sending commands, if there is no such newline character, the certificate written will be invalid.(Using the serial port assistant as an example)

4.1 For -NB /-NS model
4.1.1 Upgrade the firmware to configure TLS firmware to set the certificate
User can change device firmware to::
- Update with new features.
- Fix bugs.
Firmware and changelog can be downloaded from : Set up TLS certificate - Dropbox
Methods to Update Firmware:
- (Recommended way) OTA firmware update via BLE: Instruction.
- Update through UART TTL interface : Instruction.
4.1.2 Configure certificate
After upgrade the firmware, the serial port displays as follows:

4.1.2.1 Configure CA certificate
Please input the certificate in PEM format for the user.
Use the AT command AT+CACERT as follows:
AT+CACERT=-----BEGIN CERTIFICATE-----
MIIDQTCCAimgAwIBAgITBmyfz5m/jAo54vB4ikPmljZbyjANBgkqhkiG9w0BAQsF
ADA5MQswCQYDVQQGEwJVUzEPMA0GA1UEChMGQW1hem9uMRkwFwYDVQQDExBBbWF6
b24gUm9vdCBDQSAxMB4XDTE1MDUyNjAwMDAwMFoXDTM4MDExNzAwMDAwMFowOTEL
MAkGA1UEBhMCVVMxDzANBgNVBAoTBkFtYXpvbjEZMBcGA1UEAxMQQW1hem9uIFJv
b3QgQ0EgMTCCASIwDQYJKoZIhvcNAQEBBQADggEPADCCAQoCggEBALJ4gHHKeNXj
ca9HgFB0fW7Y14h29Jlo91ghYPl0hAEvrAIthtOgQ3pOsqTQNroBvo3bSMgHFzZM
9O6II8c+6zf1tRn4SWiw3te5djgdYZ6k/oI2peVKVuRF4fn9tBb6dNqcmzU5L/qw
IFAGbHrQgLKm+a/sRxmPUDgH3KKHOVj4utWp+UhnMJbulHheb4mjUcAwhmahRWa6
VOujw5H5SNz/0egwLX0tdHA114gk957EWW67c4cX8jJGKLhD+rcdqsq08p8kDi1L
93FcXmn/6pUCyziKrlA4b9v7LWIbxcceVOF34GfID5yHI9Y/QCB/IIDEgEw+OyQm
jgSubJrIqg0CAwEAAaNCMEAwDwYDVR0TAQH/BAUwAwEB/zAOBgNVHQ8BAf8EBAMC
AYYwHQYDVR0OBBYEFIQYzIU07LwMlJQuCFmcx7IQTgoIMA0GCSqGSIb3DQEBCwUA
A4IBAQCY8jdaQZChGsV2USggNiMOruYou6r4lK5IpDB/G/wkjUu0yKGX9rbxenDI
U5PMCCjjmCXPI6T53iHTfIUJrU6adTrCC2qJeHZERxhlbI1Bjjt/msv0tadQ1wUs
N+gDS63pYaACbvXy8MWy7Vu33PqUXHeeE6V/Uq2V8viTO96LXFvKWlJbYK8U90vv
o/ufQJVtMVT8QtPHRh8jrdkPSHCa2XV4cdFyQzR1bldZwgJcJmApzyMZFo6IQ6XU
5MsI+yMRQ+hDKXJioaldXgjUkK642M4UwtBV8ob2xJNDd2ZhwLnoQdeXeGADbkpy
rqXRfboQnoZsG4q5WTP468SQvvG5
-----END CERTIFICATE-----}
Note: Be sure to add a terminator "}" at the end of the command. Otherwise, the command will not execute successfully.
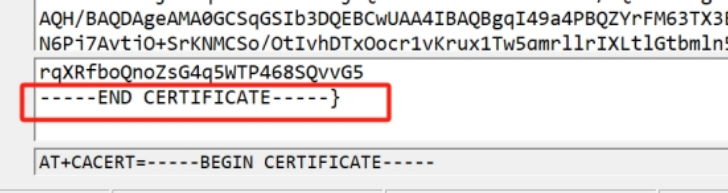
After successful execution, as shown in the following figure.

Display "Successfully configured CA certificate." If the configuration is successful, otherwise it is considered configuration failure.
4.1.2.2 Configure client certificate
Use the AT command AT+CLICERT as follows:
AT+CLICERT=-----BEGIN CERTIFICATE-----
MIIDWTCCAkGgAwIBAgIUYSpJUzfb4NTa76JJxd2th0fZA8swDQYJKoZIhvcNAQEL
BQAwTTFLMEkGA1UECwxCQW1hem9uIFdlYiBTZXJ2aWNlcyBPPUFtYXpvbi5jb20g
SW5jLiBMPVNlYXR0bGUgU1Q9V2FzaGluZ3RvbiBDPVVTMB4XDTI0MDUyNDA4MDI0
NVoXDTQ5MTIzMTIzNTk1OVowHjEcMBoGA1UEAwwTQVdTIElvVCBDZXJ0aWZpY2F0
ZTCCASIwDQYJKoZIhvcNAQEBBQADggEPADCCAQoCggEBAMTdc1GQLVBohAeCJD6n
6WTFAFrygTch90a5wUr2bhlVuDxvEhEKNcmu5vOCo5agmfLWb2VCxgezgvQOBYQ8
1oTqXJNdl4tS0DICfqb/ogVHWGHRao67XyhbPNBS0j/nCPTIIk6+/NBeYPOjaG+p
utfXE7SGIEcc3RevkYkUJx6y+WH7MLjj1mufuXBVWIL1RrfrIRPw6auVk7dhS5rU
NvYcJa7Qd6gpAh1DzPj7ZECrv7fEIIBDEsSYOy6ToWtzqGIVcIAHBDfORB0Hcm+N
7wG3KDf61P4aWkLlkP5pRUaUIQdVblxginmx2K3n8t/WP7QcfITa191rjEVVBXmk
ROsCAwEAAaNgMF4wHwYDVR0jBBgwFoAUs8Caohh1ZGP8kjSn3rtxJiJJ9IswHQYD
VR0OBBYEFCjwGwqD7FG9UCNm3wjFQX4HixzfMAwGA1UdEwEB/wQCMAAwDgYDVR0P
AQH/BAQDAgeAMA0GCSqGSIb3DQEBCwUAA4IBAQBgqI49a4PBQZYrFM63TX3EHgdd
N6Pj7AytjO+SrKNMCSo/OtIvhDTxOocr1vKrux1Tw5qmrllrIXLtlGtbmln5DS6a
DTCLrjwcIFIabLxpx5DPY1WSMYvL04SW7d4Y+3SxOFNRotDSiomr8eIIac0d3HE2
B5b0SnWZgWbrhjNUgvwo8l8tA9DOGIr2MeQ5kPjudOOiYSR3HC0v+jviBMV6VX8M
LHVH3CRshHDKBGpV1NZ1RAm9EY/oRGtSiMsyjRh6hegC0vehwVxaC4w9qG0ASkzz
42OOGfNqhYnYDiKTEIkazaoAFpTKDejWBaL7W5VpthUkQOl67IyX+ohuUKTo
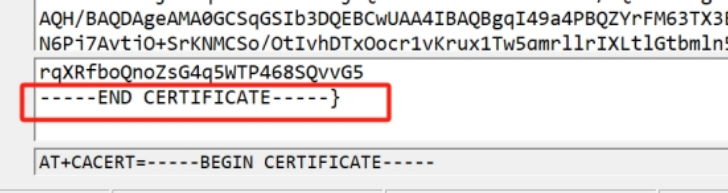
-----END CERTIFICATE-----}
Note: Be sure to add a terminator "}" at the end of the command. Otherwise, the command will not execute successfully.

Display "Successfully configured client certificate." Configuration successful, otherwise configuration failed.
4.1.2.3 Configure client private key
Use the AT command AT+CLIKEY, as shown below
AT+CLIKEY=-----BEGIN RSA PRIVATE KEY-----
MIIEpAIBAAKCAQEAxN1zUZAtUGiEB4IkPqfpZMUAWvKBNyH3RrnBSvZuGVW4PG8S
EQo1ya7m84KjlqCZ8tZvZULGB7OC9A4FhDzWhOpck12Xi1LQMgJ+pv+iBUdYYdFq
jrtfKFs80FLSP+cI9MgiTr780F5g86Nob6m619cTtIYgRxzdF6+RiRQnHrL5Yfsw
uOPWa5+5cFVYgvVGt+shE/Dpq5WTt2FLmtQ29hwlrtB3qCkCHUPM+PtkQKu/t8Qg
gEMSxJg7LpOha3OoYhVwgAcEN85EHQdyb43vAbcoN/rU/hpaQuWQ/mlFRpQhB1Vu
XGCKebHYrefy39Y/tBx8hNrX3WuMRVUFeaRE6wIDAQABAoIBAFhAOcjvjBDGuaEw
CxV3al49HfqnSZuwg0xWSztSm2qKDcwxsnSnEhO2b1vsTW9h0YGV9Vv8gg/Dvkmv
23M7XqM4+IUraJsRZbl1etdcM4KQSCOZoF4Zyv+pXuq4pf31kQNCkHaikWzLUkUG
FPQxr0vA49mCYwfd/ZL3ppM/0IWmxRwloV1Gb9q8iDBUcJGSDokZnT7diUxzzOcd
+UJ6xUhFq1v46Y7vO+73XROLv34JEBC0bIw2ErL6+AbzhHwb2mkuSccG9Ks37g3Z
dyyjjj8hm1wvHWepuWqEssaiS3HD5zAsI0v85xS8RwNj3zLfd8o1WC666n3CO+ij
VdRmR4kCgYEA+/sEFxpfaRomqcLwJebZcZH06U1RfJFfnbH2/Q6fANf8zNxwWs9A
O+jyk/CLhHYRIk6VIOMQmWwEYgJ2eAHfw2Diwj4/0eqkGu+yZOS6KTCewxSV73vc
SvACramJy4y6yEgDN5onwR1XqfVMfA0LzTcSupHR/xvrpf/gCsNFPxUCgYEAyAFd
nMUhJFSq3pOogxA43aJSkA8YuDS3jpBkKQ6vx81APpIMabQauOxFDt488TZGP3Yy
lhpa/lfFIgu2K7CgV4dUp+JtJJoZ/F+ExxUUzdqB4zxzWywAcc3RebfwP6qASwFT
G3mXYci4tgNWR+k5CSsuLXDk/OT5uo5GeGAEc/8CgYEAk6V8uxDP8STKnNRFpN/E
b6CHciDE64m/DgbWY2cq0fK9BUjxaLRhvfj8EqVzCrWnyoNjLHcAJfW+B7PLuPvY
IoJlvE1/Vb/4UnQ7ApVnY3VCwaoRRNc9uIcz+pAJ1sRqOarAf9cLDkPkNwktvM5k
KOXpSnrhIms4w/bPT18l9xUCgYBsAMDKbXEuK0JyGw5+Z/4tQQCQpnZU0rLkm3ha
64FkxaORplBprEZZ4cyQ8NW78/EPSAadI/JLMp5TejuPcDvFyGCgoBcMEuNBc1tC
HlIzr3FAgl5Qt3wt+FTMA9YKq0nINxjn10s2FKwaLccj4f9YwiaXh0VAg22PnlDT
pBYDhQKBgQCMwyKXJ4zYiDRdvLvgKzeuKaU4KNQItHE4KORPfkecjPoENt4bKxDw
2EdNFQLIoqBHL1s+/8+SzhCI31V7pkTs1AqCxDExJS7+8Z5NQFQIo/jooUo0N80E
y3ZZS6OLOXXscEqhMogf1grfbabXM9OkgTIq43cPQHtMGQiFAtIJkg==
-----END RSA PRIVATE KEY-----}
Note: Be sure to add a terminator "}" at the end of the command. Otherwise, the command will not execute successfully.
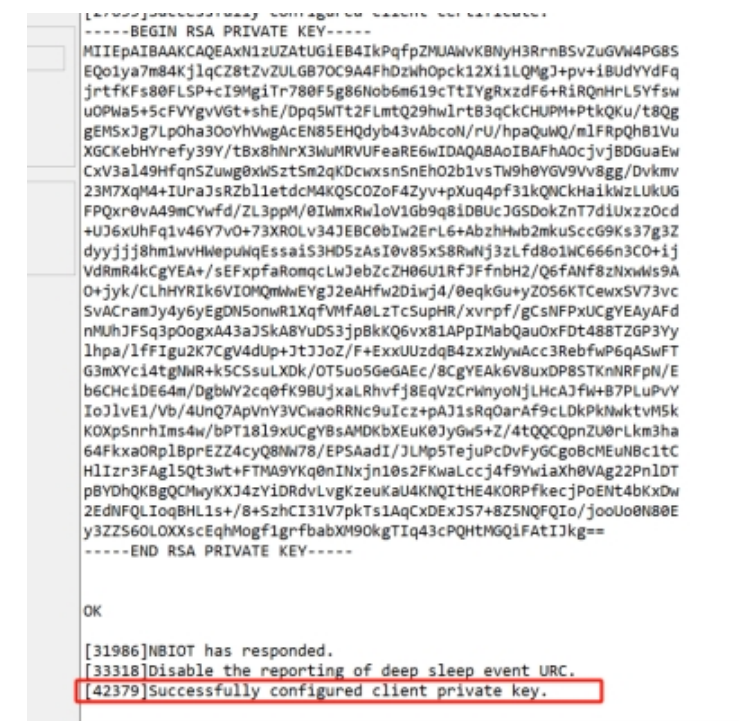
Display "Successfully configured client private key." If the configuration is successful, otherwise it is considered configuration failure.
4.1.2.4 Re-upgrade the firmware
After completing the certificate configuration, Burn the bootloader firmware first, then re-burn the original working firmware.
4.1.2.5 Clear Certificates by Overwriting (For -NB/-NS Modules)
The -NB/-NS modules (BC660K) do not support clearing certificates via AT commands or firmware updates.
To effectively remove existing certificates, users may overwrite them with dummy data.
1.Flash the certificate-provisioning firmware: Set up TLS certificate - Dropbox
2. Use the standard AT commands (AT+CACERT, AT+CLICERT, AT+CLIKEY) to write non-certificate data (e.g., random strings like 123456).
Example:
AT+CACERT=123456}
AT+CLICERT=123456}
AT+CLIKEY=123456}
3. Check for success responses after each command:

(If you get "Failure", retry or check module connectivity.)
4.2 For -CB /-CS model
4.2.1 Upgrade the firmware to configure TLS firmware to set the certificate
User can change device firmware to::
- Update with new features.
- Fix bugs.
Firmware and changelog can be downloaded from : Set up TLS certificate - Dropbox
Methods to Update Firmware:
- Update through UART TTL interface : Instruction.
4.2.2 Configure certificate
After upgrade the firmware, the serial port displays as follows:

4.2.2.1 Configure CA certificate
Note:You should select one of the certificates.Either CA1 or CA3 can be used
Please input the certificate in PEM format for the user.
Use the AT command AT+CACERT as follows:
AT+CACERT=-----BEGIN CERTIFICATE-----
MIIDQTCCAimgAwIBAgITBmyfz5m/jAo54vB4ikPmljZbyjANBgkqhkiG9w0BAQsF
ADA5MQswCQYDVQQGEwJVUzEPMA0GA1UEChMGQW1hem9uMRkwFwYDVQQDExBBbWF6
b24gUm9vdCBDQSAxMB4XDTE1MDUyNjAwMDAwMFoXDTM4MDExNzAwMDAwMFowOTEL
MAkGA1UEBhMCVVMxDzANBgNVBAoTBkFtYXpvbjEZMBcGA1UEAxMQQW1hem9uIFJv
b3QgQ0EgMTCCASIwDQYJKoZIhvcNAQEBBQADggEPADCCAQoCggEBALJ4gHHKeNXj
ca9HgFB0fW7Y14h29Jlo91ghYPl0hAEvrAIthtOgQ3pOsqTQNroBvo3bSMgHFzZM
9O6II8c+6zf1tRn4SWiw3te5djgdYZ6k/oI2peVKVuRF4fn9tBb6dNqcmzU5L/qw
IFAGbHrQgLKm+a/sRxmPUDgH3KKHOVj4utWp+UhnMJbulHheb4mjUcAwhmahRWa6
VOujw5H5SNz/0egwLX0tdHA114gk957EWW67c4cX8jJGKLhD+rcdqsq08p8kDi1L
93FcXmn/6pUCyziKrlA4b9v7LWIbxcceVOF34GfID5yHI9Y/QCB/IIDEgEw+OyQm
jgSubJrIqg0CAwEAAaNCMEAwDwYDVR0TAQH/BAUwAwEB/zAOBgNVHQ8BAf8EBAMC
AYYwHQYDVR0OBBYEFIQYzIU07LwMlJQuCFmcx7IQTgoIMA0GCSqGSIb3DQEBCwUA
A4IBAQCY8jdaQZChGsV2USggNiMOruYou6r4lK5IpDB/G/wkjUu0yKGX9rbxenDI
U5PMCCjjmCXPI6T53iHTfIUJrU6adTrCC2qJeHZERxhlbI1Bjjt/msv0tadQ1wUs
N+gDS63pYaACbvXy8MWy7Vu33PqUXHeeE6V/Uq2V8viTO96LXFvKWlJbYK8U90vv
o/ufQJVtMVT8QtPHRh8jrdkPSHCa2XV4cdFyQzR1bldZwgJcJmApzyMZFo6IQ6XU
5MsI+yMRQ+hDKXJioaldXgjUkK642M4UwtBV8ob2xJNDd2ZhwLnoQdeXeGADbkpy
rqXRfboQnoZsG4q5WTP468SQvvG5
-----END CERTIFICATE-----}
Note: Be sure to add a terminator "}" at the end of the command. Otherwise, the command will not execute successfully.
After successful execution, as shown in the following figure.
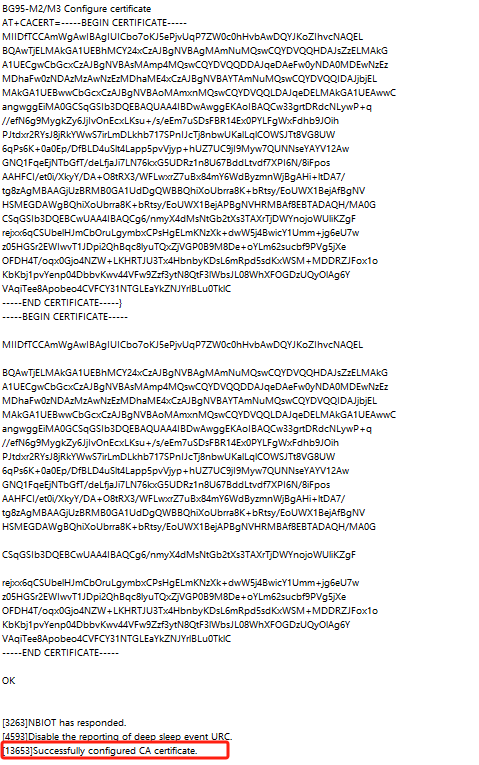
Display "Successfully configured CA certificate." If the configuration is successful, otherwise it is considered configuration failure.
4.2.2.2 Configure client certificate
Use the AT command AT+CLICERT as follows:
AT+CLICERT=-----BEGIN CERTIFICATE-----
MIIDWTCCAkGgAwIBAgIUYSpJUzfb4NTa76JJxd2th0fZA8swDQYJKoZIhvcNAQEL
BQAwTTFLMEkGA1UECwxCQW1hem9uIFdlYiBTZXJ2aWNlcyBPPUFtYXpvbi5jb20g
SW5jLiBMPVNlYXR0bGUgU1Q9V2FzaGluZ3RvbiBDPVVTMB4XDTI0MDUyNDA4MDI0
NVoXDTQ5MTIzMTIzNTk1OVowHjEcMBoGA1UEAwwTQVdTIElvVCBDZXJ0aWZpY2F0
ZTCCASIwDQYJKoZIhvcNAQEBBQADggEPADCCAQoCggEBAMTdc1GQLVBohAeCJD6n
6WTFAFrygTch90a5wUr2bhlVuDxvEhEKNcmu5vOCo5agmfLWb2VCxgezgvQOBYQ8
1oTqXJNdl4tS0DICfqb/ogVHWGHRao67XyhbPNBS0j/nCPTIIk6+/NBeYPOjaG+p
utfXE7SGIEcc3RevkYkUJx6y+WH7MLjj1mufuXBVWIL1RrfrIRPw6auVk7dhS5rU
NvYcJa7Qd6gpAh1DzPj7ZECrv7fEIIBDEsSYOy6ToWtzqGIVcIAHBDfORB0Hcm+N
7wG3KDf61P4aWkLlkP5pRUaUIQdVblxginmx2K3n8t/WP7QcfITa191rjEVVBXmk
ROsCAwEAAaNgMF4wHwYDVR0jBBgwFoAUs8Caohh1ZGP8kjSn3rtxJiJJ9IswHQYD
VR0OBBYEFCjwGwqD7FG9UCNm3wjFQX4HixzfMAwGA1UdEwEB/wQCMAAwDgYDVR0P
AQH/BAQDAgeAMA0GCSqGSIb3DQEBCwUAA4IBAQBgqI49a4PBQZYrFM63TX3EHgdd
N6Pj7AytjO+SrKNMCSo/OtIvhDTxOocr1vKrux1Tw5qmrllrIXLtlGtbmln5DS6a
DTCLrjwcIFIabLxpx5DPY1WSMYvL04SW7d4Y+3SxOFNRotDSiomr8eIIac0d3HE2
B5b0SnWZgWbrhjNUgvwo8l8tA9DOGIr2MeQ5kPjudOOiYSR3HC0v+jviBMV6VX8M
LHVH3CRshHDKBGpV1NZ1RAm9EY/oRGtSiMsyjRh6hegC0vehwVxaC4w9qG0ASkzz
42OOGfNqhYnYDiKTEIkazaoAFpTKDejWBaL7W5VpthUkQOl67IyX+ohuUKTo
-----END CERTIFICATE-----}
Note: Be sure to add a terminator "}" at the end of the command. Otherwise, the command will not execute successfully.

Display "Successfully configured client certificate." Configuration successful, otherwise configuration failed.
4.2.2.3 Configure client private key
Use the AT command AT+CLIKEY, as shown below
AT+CLIKEY=-----BEGIN RSA PRIVATE KEY-----
MIIEpAIBAAKCAQEAxN1zUZAtUGiEB4IkPqfpZMUAWvKBNyH3RrnBSvZuGVW4PG8S
EQo1ya7m84KjlqCZ8tZvZULGB7OC9A4FhDzWhOpck12Xi1LQMgJ+pv+iBUdYYdFq
jrtfKFs80FLSP+cI9MgiTr780F5g86Nob6m619cTtIYgRxzdF6+RiRQnHrL5Yfsw
uOPWa5+5cFVYgvVGt+shE/Dpq5WTt2FLmtQ29hwlrtB3qCkCHUPM+PtkQKu/t8Qg
gEMSxJg7LpOha3OoYhVwgAcEN85EHQdyb43vAbcoN/rU/hpaQuWQ/mlFRpQhB1Vu
XGCKebHYrefy39Y/tBx8hNrX3WuMRVUFeaRE6wIDAQABAoIBAFhAOcjvjBDGuaEw
CxV3al49HfqnSZuwg0xWSztSm2qKDcwxsnSnEhO2b1vsTW9h0YGV9Vv8gg/Dvkmv
23M7XqM4+IUraJsRZbl1etdcM4KQSCOZoF4Zyv+pXuq4pf31kQNCkHaikWzLUkUG
FPQxr0vA49mCYwfd/ZL3ppM/0IWmxRwloV1Gb9q8iDBUcJGSDokZnT7diUxzzOcd
+UJ6xUhFq1v46Y7vO+73XROLv34JEBC0bIw2ErL6+AbzhHwb2mkuSccG9Ks37g3Z
dyyjjj8hm1wvHWepuWqEssaiS3HD5zAsI0v85xS8RwNj3zLfd8o1WC666n3CO+ij
VdRmR4kCgYEA+/sEFxpfaRomqcLwJebZcZH06U1RfJFfnbH2/Q6fANf8zNxwWs9A
O+jyk/CLhHYRIk6VIOMQmWwEYgJ2eAHfw2Diwj4/0eqkGu+yZOS6KTCewxSV73vc
SvACramJy4y6yEgDN5onwR1XqfVMfA0LzTcSupHR/xvrpf/gCsNFPxUCgYEAyAFd
nMUhJFSq3pOogxA43aJSkA8YuDS3jpBkKQ6vx81APpIMabQauOxFDt488TZGP3Yy
lhpa/lfFIgu2K7CgV4dUp+JtJJoZ/F+ExxUUzdqB4zxzWywAcc3RebfwP6qASwFT
G3mXYci4tgNWR+k5CSsuLXDk/OT5uo5GeGAEc/8CgYEAk6V8uxDP8STKnNRFpN/E
b6CHciDE64m/DgbWY2cq0fK9BUjxaLRhvfj8EqVzCrWnyoNjLHcAJfW+B7PLuPvY
IoJlvE1/Vb/4UnQ7ApVnY3VCwaoRRNc9uIcz+pAJ1sRqOarAf9cLDkPkNwktvM5k
KOXpSnrhIms4w/bPT18l9xUCgYBsAMDKbXEuK0JyGw5+Z/4tQQCQpnZU0rLkm3ha
64FkxaORplBprEZZ4cyQ8NW78/EPSAadI/JLMp5TejuPcDvFyGCgoBcMEuNBc1tC
HlIzr3FAgl5Qt3wt+FTMA9YKq0nINxjn10s2FKwaLccj4f9YwiaXh0VAg22PnlDT
pBYDhQKBgQCMwyKXJ4zYiDRdvLvgKzeuKaU4KNQItHE4KORPfkecjPoENt4bKxDw
2EdNFQLIoqBHL1s+/8+SzhCI31V7pkTs1AqCxDExJS7+8Z5NQFQIo/jooUo0N80E
y3ZZS6OLOXXscEqhMogf1grfbabXM9OkgTIq43cPQHtMGQiFAtIJkg==
-----END RSA PRIVATE KEY-----}
Note: Be sure to add a terminator "}" at the end of the command. Otherwise, the command will not execute successfully.
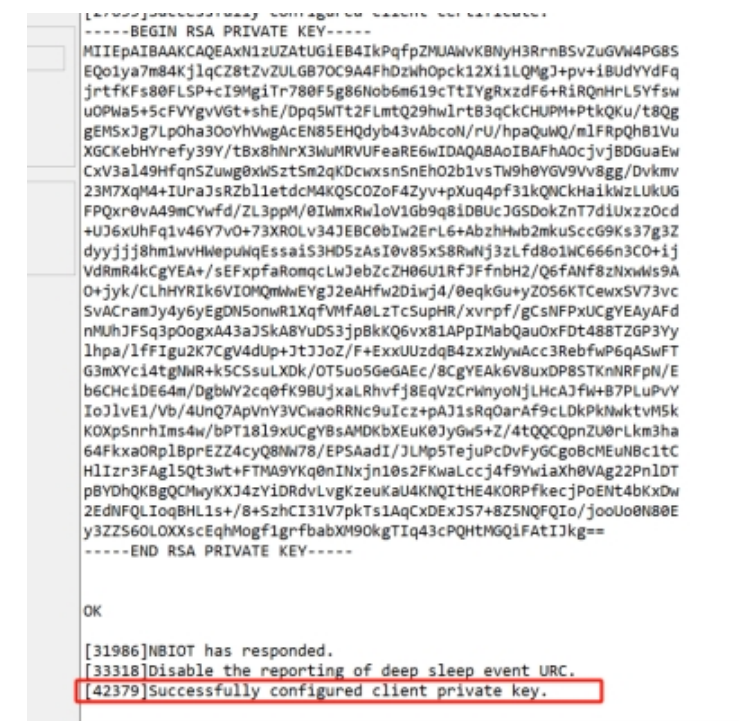
Display "Successfully configured client private key." If the configuration is successful, otherwise it is considered configuration failure.
4.2.2.4 Re-upgrade the firmware
After completing the certificate configuration, Burn the bootloader firmware first, then re-burn the original working firmware.
4.2.2.5 For -CB /-CS model Certificate setting error/change certificate
When you set the wrong certificate or you need to re-set another certificate.
Please use the following three commands:
AT+DELCLIKEY}
AT+DELCLICERT}
AT+DELCACERT}
Note: 1.When there is no certificate on the device, a deletion error will be displayed.
2.When the device already has a certificate, using the command to configure the certificate again will display a configuration error.
5. Configure draginoNB-device
5.1 Configure the data format sent by the device
AT+PRO=3,5 (Data is in Json format of MQTT)
5.2 Set server address
AT+SERVADDR=an5tk94sdgjat-ats.iot.us-east-1.amazonaws.com,8883
5.3 Set up private and public topics
AWS does not limit topics, so you can set any topic
AT+SUBTOPIC=Any
AT+PUBTOPIC=Any
5.4 Set the TLS mode
AT+TLSMOD=1,2
To use the TLS mode certificate function, users need to configure the AT+TLSMOD command.
AT+TLSMOD=1,0 // No authentication
AT+TLSMOD=1,1 // Perform server authentication
AT+TLSMOD=1,2 // Perform server and client authentication if requested by the remote server.(In AWS we recommend using this mode)
5.5 Set the MQOS
AT+MQOS=XX (Depends on your server configuration)
Please find it in AWS's MQTT test client

5.6 Restart the device
6. View data on AWS
6.1 Find MQTT test client in test
In the fourth step, fill in the topics you subscribed to before
AT+PUBTOPIC=XXXX
If you forget your previous topic, you can fill in #,subscribe to all topics

6.2 The data published information in Subscriptions


