Remote Access Gateway
Table of Contents:
- 1. Use Remote.it service
- 2. RSSH Introduction
- 2.1 For Firmware Version lower than lgw--build-v5.4.1616478814-20210323-1355
- 2.2 For Firmware Version higher than lgw--build-v5.4.1618196981-20210412-1111
1. Use Remote.it service
Remote.it for remote access is available in the latest Dragino firmware for gateway. For security concerns, the remote.it only available base on end-user demand.
Important Notice:
- Remote.it access will give full control of your device to remote support.
- The Remote.it allow Dragino Support to remote access to the device, If user want to access himself, it need to sign up for an remote.it account.
For how to use remoteit, please see : Remoteit user instruction for Dragino Gateway.
2. RSSH Introduction
Reverse SSH for remote access is available in the latest Dragino firmware for gateway. For security concern, the RSSH only available base on end user demand.
Important Notice:
- RSSH access will give full control of your device to remote support. Please remove sensitivity info before perform this
- This RSSH allow Dragino Support to remote access to the device, If user want to access himself, he need to set up the RSSH server himself.
Below gateway support reverse SSH access:
- Firmware Version > LG02_LG08-5.3.1580178039 Firmware Download
- LG01N, OLG01N (Note: LG01-P LG01-S doesn't support)
- LG02, OLG02
- LG308, DLOS8
- LPS8
- LIG16
- MS14 series if installed with the same firmware.
2.1 For Firmware Version lower than lgw--build-v5.4.1616478814-20210323-1355
2.1.1 End User Guide to use SSH access
Go to this the Reverse SSH page as below:
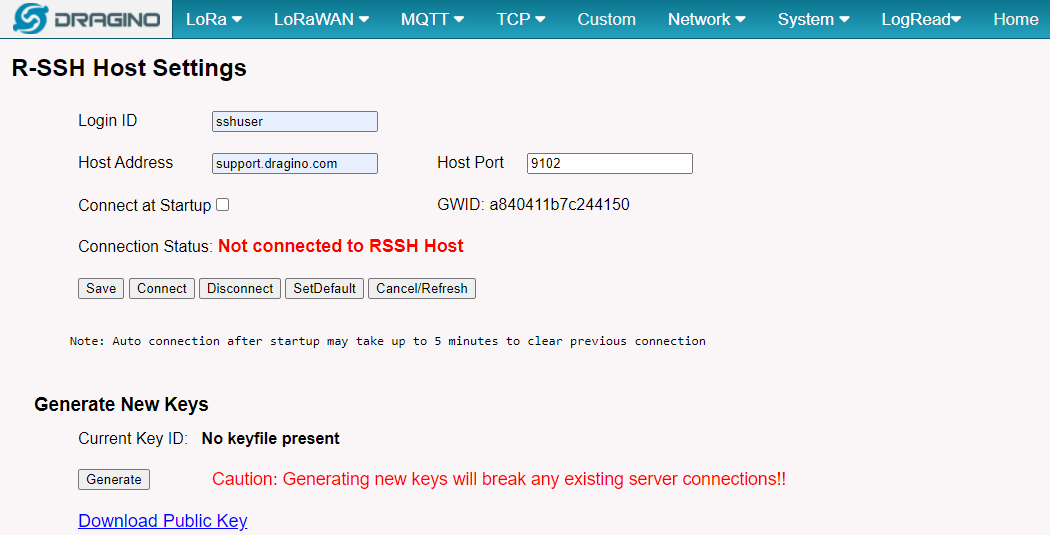
Get the RSSH configure page
Connection OK.
- Login ID: Input sshuser
- Host Address: Input support.dragino.com
- Host Port: Please email to support @ dragino.com to get a valid host port.
- Connect at Startupt: Choose to enable connect once device is powered.
- Network Keys: Click the Generate keys to generate the keys and download / mail it to Dragino support so Dragino can prepare the remote access to
After doing above, please download and mail the public keys to Dragino support and wait for our mail for the valid host port. Input the valid host port got from our support and click connect so we can remote access to your gateway.
2.1.2 How to Ser up a Reverse SSH access
Advance administrator can config a SSH server to provide support their end user themselves. Instruction is as below:
- Prepare a Linux server with public IP. The gateways need to be able to create SSH connection to this server. We recommend to use a server that performs no other function than to support the RSSH access, and to have no additional accounts active, and no access from the Internet that uses ID/password authentication.
- In the gateway settings, The Login ID will be the SSH user for this server and the Host Address is the server address.
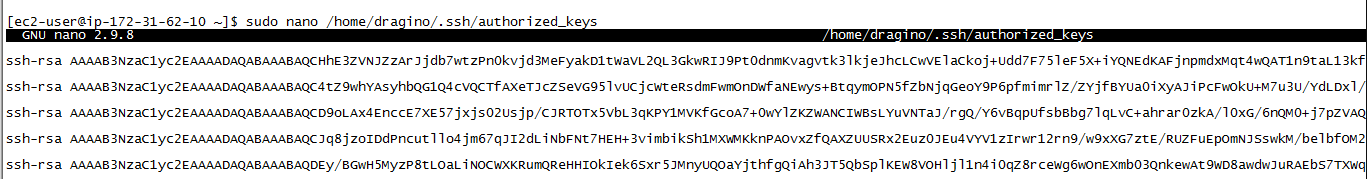
- Ask your end user to send you the key generate in the gateway and put them in /home/<Login ID>/.ssh/authorized_key file.
- Give a free port to the user and ask them to configure RSSH page in the gateway.
- In your server or other machine, you will able to access to the end user device by below command:
$ ssh -p <End User Host Port> root@<Host Address>
Remote RSSH Access allow the gateway to connect to SSH server as well. This will create risk to the RSSH server. Please make sure the account use for Gateway Access has the lowest access right.
Note for set up RSSH server
If gateway reboot or the connection is incidentely close by end node. The port in SSH server will still be occupy for a long time. Administrator can use below commands to release the port.
[root@iZt4n22vqvm7ajogrfiif6Z ~]# lsof -i :9102 --> check the port 9102 process status (change 9102 to the actually port for your gateway.
COMMAND PID USER FD TYPE DEVICE SIZE/OFF NODE NAME
sshd 21430 sshuser 15u IPv4 47567059 0t0 TCP localhost:bacula-fd (LISTEN)
[root@iZt4n22vqvm7ajogrfiif6Z ~]# kill 21430 --> Kill PID of this process.
[root@iZt4n22vqvm7ajogrfiif6Z ~]# lsof -i :9102
[root@iZt4n22vqvm7ajogrfiif6Z ~]#
2.2 For Firmware Version higher than lgw--build-v5.4.1618196981-20210412-1111
Below gateway support reverse SSH access:
Firmware Version >lgw--build-v5.4.1618196981-20210412-1111 Firmware Download
LG01N, OLG01N (Note: LG01-P LG01-S doesn't support)
LG02, OLG02
LG308, DLOS8
LPS8
LIG16
2.2.1 End User Guide to use SSH access
2.2.1.1 Install the SSH service for server
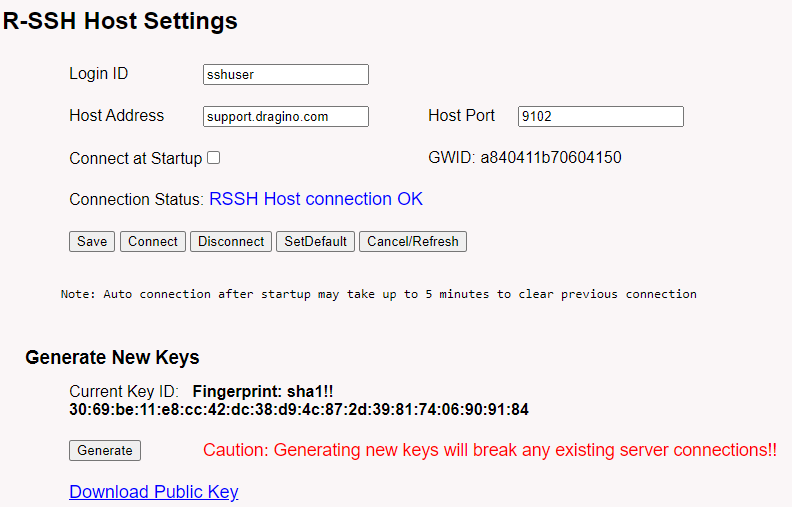
Step 1 : Download the SSH service code
1). git clone https://github.com/dragino/rssh-server.git rssh-server
git clone rssh-server
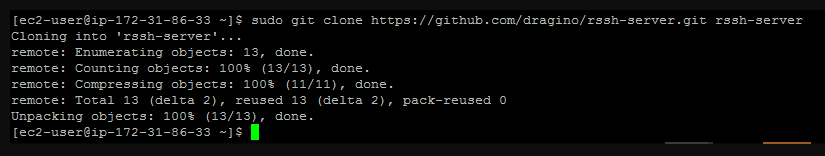
2). cd rssh-server; sudo make ---> to Generate the execute file:rssh_serv
Generate the execute file
Debug :
if you git fail. --> sudo: git: command not found.
please install git. --> yum install git -y or apt-get install git -y.
if you make error 127,it lack of gcc.
please install gcc. --> yum install gcc.
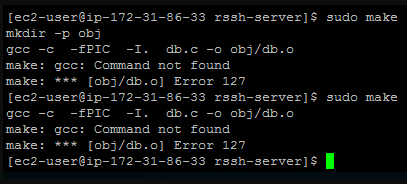
lack of gcc
if you make a fatal error : sqlite3.h,it lack of sqlite3.
please insatell sqlite3.
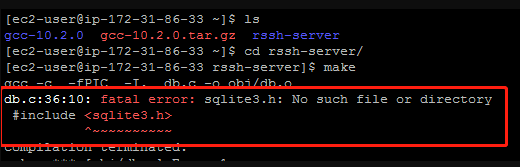
lack of sqlite3
How to install Sqlit3:
Step1: Download the SQLit3 installation package
sudo wget https://www.sqlite.org/2021/sqlite-autoconf-3350400.tar.gz
Step2: tar the SQLit3 installation package
sudo tar -zxvf sqlite-autoconf-3350300.tar.gz
Step3: Generate the makefile
cd sqlite-autoconf-3350300/;./configure
Step4: Compile makefile
sudo make
Step5: Install makefile
sudo make install
Check:
cd /usr/local/bin;ls -al --> Check to see if there is a file for sqlite3
cd sqlite-autoconf-3350300/;./sqlite3 test.db --> Test whether the sqlite3 was installed successfully
debug:
If you get the imformation that is SQLite header and source version mismatch, when you execute./sqlite3 test.db.
Please execute the command /sbin/ldconfig.
After that execute the command ./sqlite3 test.db again.
Step 2 : Install and run the RSS service
1): intall database for /var/rsshdb.sqlite3 and Server development port for 3721(The default is 3721)
user must enter the root account and run the following commands
$ ./create_sqlite3_db.sh
$ ./rssh_serv -p 3721 2>&1 &
$ ps -ef | grep rssh_serv check 3721 port
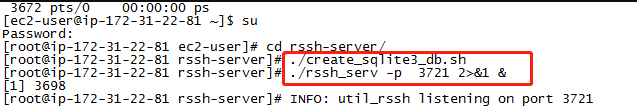
intall database and server development port
Debug:
Check /var/rsshdb.sqlite3 --> ls /var/rsshdb.sqlite3
Check ls /var/rsshdb.sqlite3 --> sudo chmod 777 rssh_serv
if fail to open dpvlry or to bind to it
please kill rssh_serv,and run ./rssh_serv -p 3721 2>&1 & again
Step 3 : Create a minimal SSH user (reverse SSH proxy for the gateway)
1): sudo useradd XXXXX (custom user name)
2): sudo passwd xxxxxx
3): cp /bin/bash /bin/rbash
4): sudo nano /etc/passwd --> Change /bin/bash to /bin/rbash
5): sudo nano /home/xxxxx/.bashrc empty it,and input export PATH=$HOME/bin
6): sudo nano /home/xxxxx/.bash_profile empty it,and input export PATH=$HOME/bin
Now user "XXXXX" is the user with limited permissions of the current system
2.2.2 How does user get the gateway to connect to a user's private server
Step 1 : Come bace the gateway web UI for get the gateway Public key
1) in the system --> Remote Mgmt
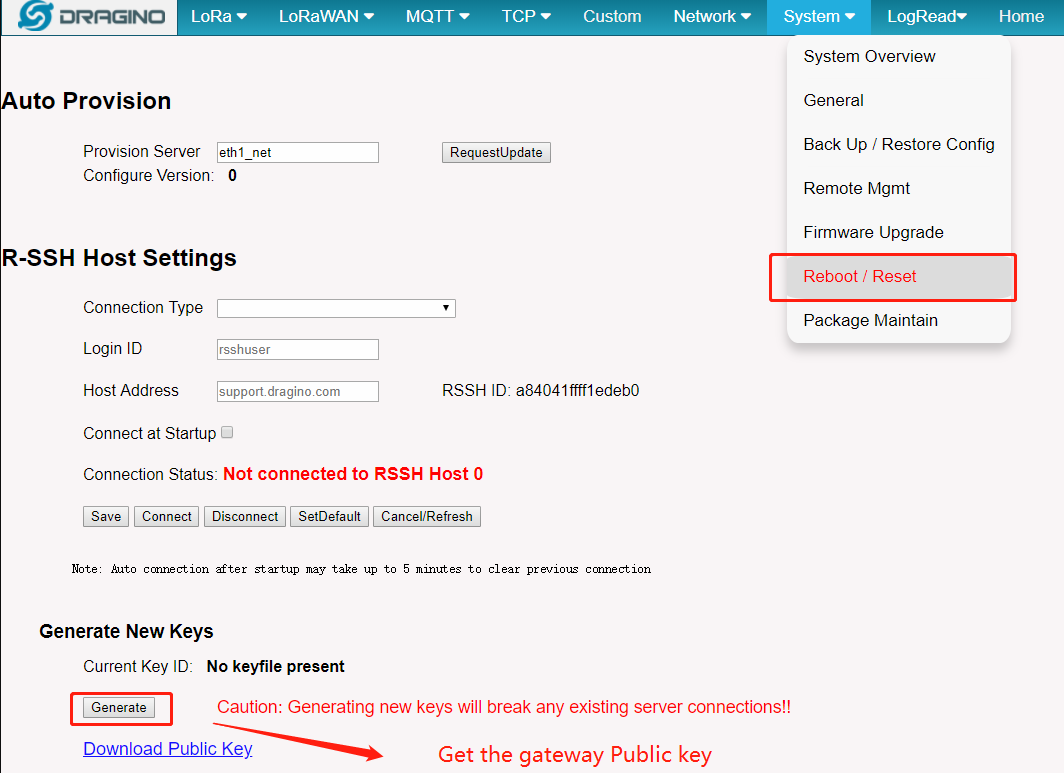
Remote Mgmt
Step 2 : Authorization server
copy the Gateway Publickey into user's private server "/home/XXXXX/.ssh/authorized_keys" file.
Publickey
Step 3 : connecte private server
in the gateway web UI
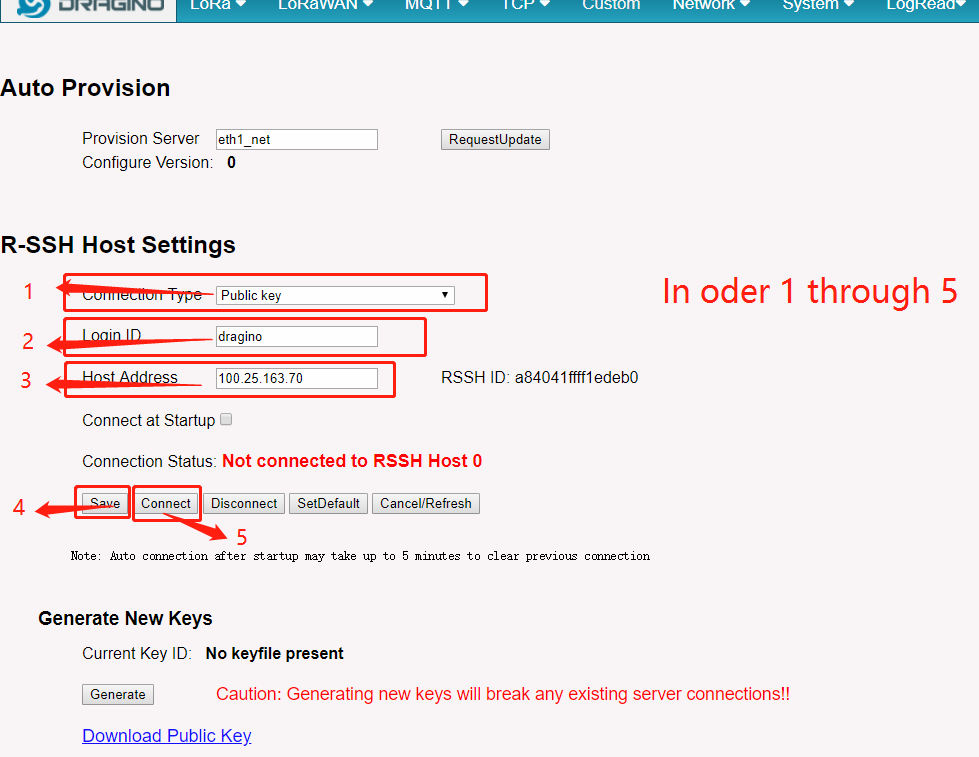
gateway web UI
Connection Type : If user's least privileged user with private server uses a password, select Public Key
Note: if user's least privileged user no uses a password,choose from both is fine
Login ID : Input user name "eg : "XXXXX"
Host Address : Input user's private server address
Connect at Startupt : Choose to enable connect once device is powered.
Click Save and then Connect
Step 4 : Cheak is fine
Rssh Host connection Ok
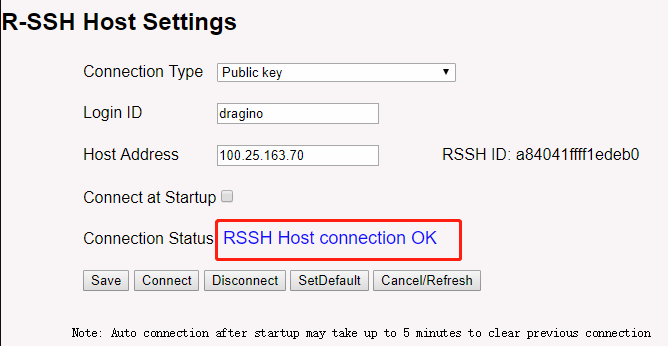
Rssh Host connection Ok
user can use common ps | grep ssh to check it in the gateway.
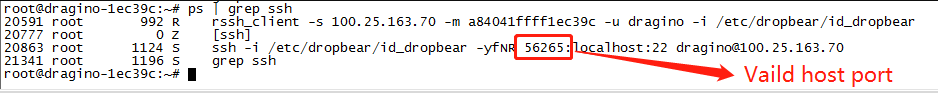
Check the gateway
Step 5 : Create an authorization key file
1): sudo mkdir /home/xxxxx/.ssh; sudo touch /home/xxxxx/.ssh/authorizedkey
Debug:
check: sudo ls /home/xxxxx/.ssh/authorizedkey
2.2.3 How to Ser up a Reverse SSH access
Step 1 : Log into the server system
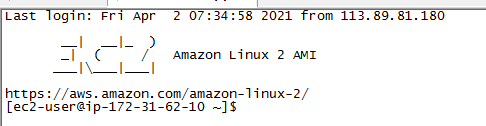
Loging server
Step 2 : access the gateway
$ cd rssh-server/
Check the gateway linking to the server $ ./connect-gw.sh -l
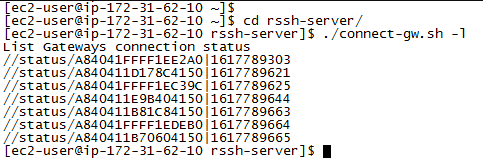
Check the gateway linking to the server
access the gateway $ ./connect-gw.sh <GWID>
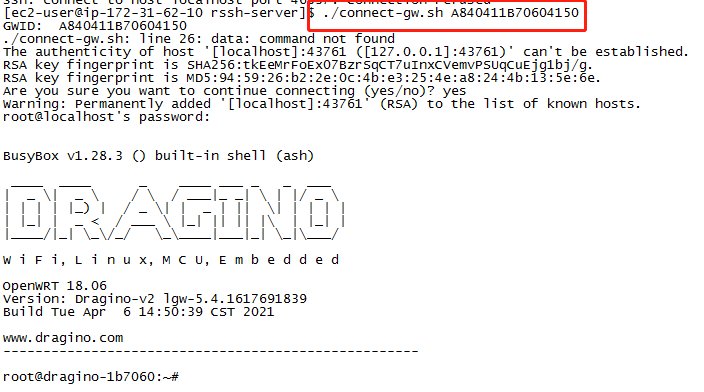
reverse ssh access the gateway
